
OT Security: Minimize Cyber Risks in Production & Co.
Security strategies for Industry 4.0 and networked OT systems
OT Security as Accompanying Protection for the Digital Transformation of Operational Systems
Networked production facilities, IoT devices and Industry 4.0 technologies are part of industrial digitalization. They increase efficiency, but also entail new cyber risks. Operational technology (OT) includes a wide variety of control systems (ICS), such as those used in production facilities, power plants or logistics centers. In contrast to traditional IT, OT systems are often in operation for decades and difficult to update - an attractive target for cyber criminals. At the same time, regulatory requirements such as the NIS2 directive oblige KRITIS operators to detect attacks. Secure your OT and IoT environments professionally with Arvato Systems.
Arvato Systems: Your Partner for Holistic OT Security
The boundaries between IT and OT networks are becoming increasingly blurred, which increases the risk of security incidents. That's why Arvato Systems takes a holistic approach: We look at your business processes and identify the critical areas - usually SAP systems or production facilities. We then develop customized security strategies. By using solutions such as Microsoft Defender for IoT, we ensure seamless integration into security systems such as Microsoft Sentinel or other SIEM systems. This solution provides real-time data exchange for resource discovery, security risk management, and protection against cyber threats.
Advantages in the Area of OT Security

OT security is not just about technology, but also about protecting business-critical processes. Many companies underestimate the risks of outdated systems and a lack of segmentation. With a holistic approach, we not only secure networks, but the entire operation.
Process
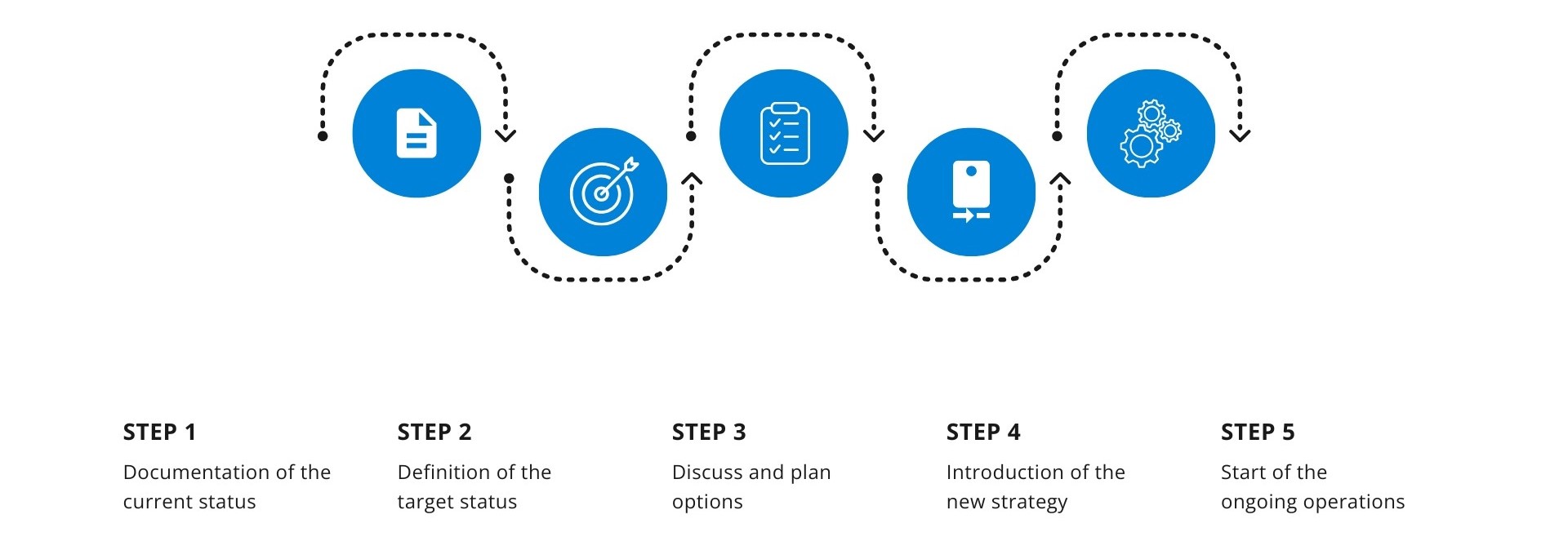
Our Approach for Your OT Security
To optimally secure your OT environment, we follow a structured approach that is divided into five phases:
We start with a detailed inventory of your OT systems. We take into account that OT environments have different requirements than traditional IT infrastructures. Typical threats such as phishing are less relevant here; instead, the focus is on risks such as unsecured remote access by maintenance companies or the improper handling of physical media such as USB sticks.
Based on the analysis, we develop a customized security concept. This includes the definition of security guidelines, the implementation of access controls and the segmentation of networks, which ensures the separation of IT and OT areas.
In this phase, we implement the defined measures. These include the installation of security solutions, the configuration of firewalls and the establishment of monitoring systems that are specifically tailored to the requirements of your OT environment.
Our 24/7 Security Operations Center (SOC) takes over the continuous monitoring of your OT systems. With Managed Detection and Response (MDR), we identify anomalies at an early stage and can respond immediately if necessary to neutralize potential threats.
The threat landscape is constantly evolving. That's why we regularly evaluate the effectiveness of the security measures implemented and adapt them if necessary. Our solutions are scalable and grow with your requirements, ensuring that your OT infrastructure is effectively protected in the long term.
Industry-Specific IoT and OT Security Solutions from the Experts
Every industry has its specific challenges in OT security. Energy suppliers, for example, need to secure their grid control systems against targeted cyberattacks to ensure a stable supply. In the manufacturing industry, on the other hand, remote maintenance access in particular represents a critical gateway for attacks. Smart warehouses, on the other hand, are increasingly at risk from unsecured IoT sensors, which offer attack surfaces for hackers. In building technology, cyber attacks on networked systems such as climate control systems can also lead to massive operational disruptions. With our many years of experience in securing complex OT and IoT infrastructures, we develop customized security solutions that are precisely tailored to your individual requirements.
Frequently Asked Questions About OT Security
-
What are the particular challenges in OT security?
OT systems are often decades old and not designed for modern cybersecurity. In addition, there is often a lack of clear separation between IT and OT networks, which increases security risks.
-
How does OT security differ from classic IT security?
While IT security prioritizes the protection of data and systems, the focus of OT security is on the operational reliability and availability of physical processes. Security updates are often difficult to implement, which is why other protective measures are necessary.
-
What role does Microsoft Defender for IoT play in OT security?
Microsoft Defender for IoT provides real-time resource discovery, security risk management and cyber threat protection specifically for IoT and OT devices. It is not a stand-alone security solution, but is used for network monitoring and enables data exchange between connected devices and additional security systems such as Microsoft Sentinel or third-party SIEM/SOAR tools.
-
How can I secure my OT infrastructure without disrupting operations?
A combination of segmented networks, zero-trust access models and passive threat detection can improve OT security without disrupting production processes. Technologies such as network sensors and security monitoring enable protective measures to be taken without directly interfering with ongoing processes.
-
What are the advantages of 24/7 monitoring by a Security Operations Center (SOC)?
A SOC ensures continuous monitoring and a rapid response to security incidents. Anomalies can be detected at an early stage, which minimizes potential damage.
Your Contact for OT Security



